


Cybercrime To Soar in the Next Five Years
According to new estimates from Statista’s Cybersecurity Outlook, the worldwide cost of cybercrime is expected to soar. Statista estimates cybercrime’s fiscal damage to rise from $8.44 trillion in 2022 to $23.84 trillion by 2027, nearly tripling in only...
Don’t Let Hackers Disrupt Your Holiday
Year after year, the holiday season brings a heightened threat of cybercrime. Bad actors are on the search to exploit any security vulnerability they can find. Hackers look for – and always find – the most vulnerable companies to target. It’s no...
Twitter’s cybersecurity troubles continue with ‘serious risk of breach’
The chaos continues at Elon Musk’s Twitter, with cybersecurity troubles mounting. Security experts and whistleblowers have warned of a new company environment that is severely undercutting defenses, leading to potential consequences for both Twitter HQ and the...
15,000+ WordPress Sites Compromised in Hostile SEO Scheme
Cybercriminals have successfully launched a malicious black hat search engine optimization (SEO) campaign, redirecting website visitors to fake Q&A portals. This hostile SEO scheme can be “described as malware designed to hijack a website in order to abuse...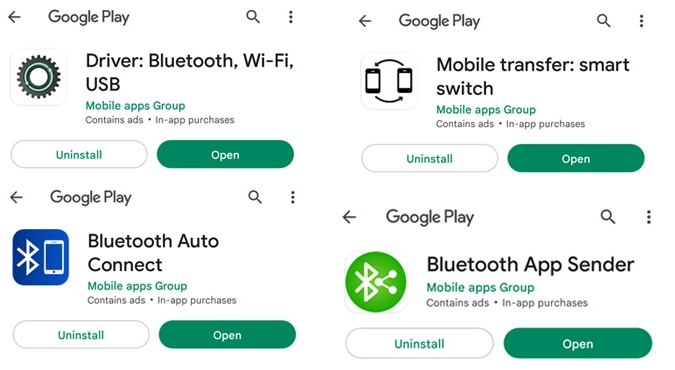
Scam of the Week: Android Apps Redirect Users to Malicious Sites
Recently uncovered by cybersecurity researchers, a set of four Android apps have been found to link users to malicious sites. These malicious sites either install adware or attempt to steal information from the user, in what has found to be a massive cybercrime...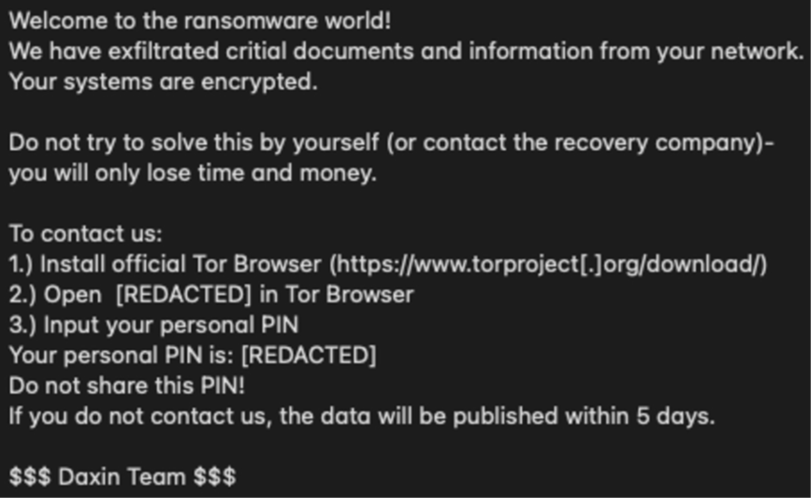
CISA Unveils Daixin Team Hacking Efforts into Healthcare Organizations
As a part of their #StopRansomware campaign, the Cybersecurity Advisory (CSA) regularly publishes advisories for network defenders that “detail various ransomware variants and ransomware threat actors”. The stopransomware.gov website was created as a...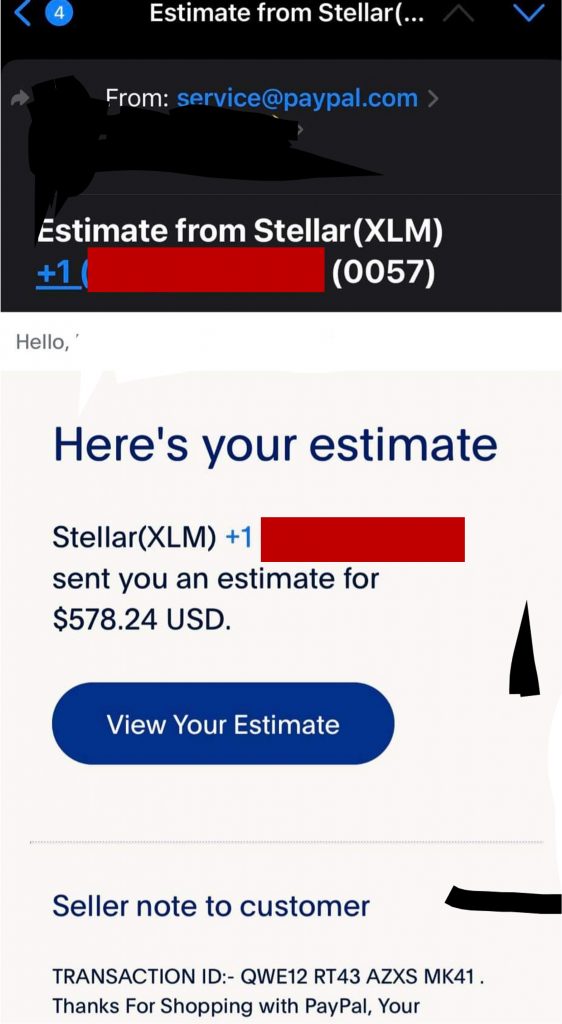
Scam of the Week: PayPal Crypto Invoice Scam
Fraudsters on the Internet have found a new method for stealing cash from ordinary people. Disguising their fraudulent activity as legitimate invoices, scammers pose as PayPal sellers requesting invoices for cryptocurrencies. These include popular cryptocurrencies...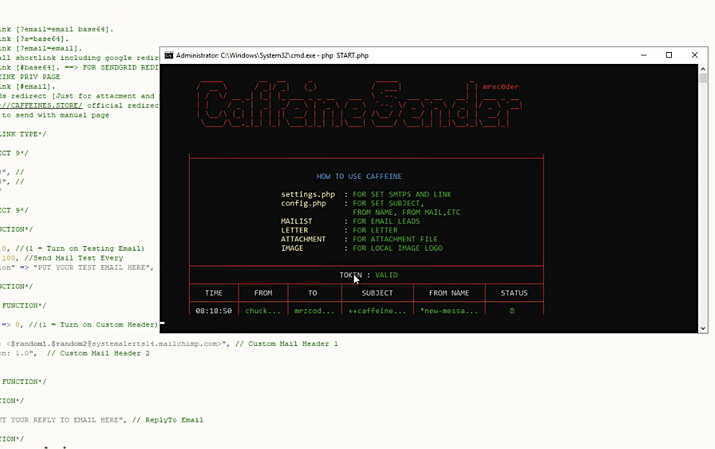
Researchers uncover phishing-as-a-service platform Caffeine
Recently unearthed by security researchers, a new, criminal ‘phishing-as-a-service’ (PhaaS) platform has been identified. This phishing platform, called Caffeine, is unique in its broad accessibility. Anyone with an email can create an account, choosing...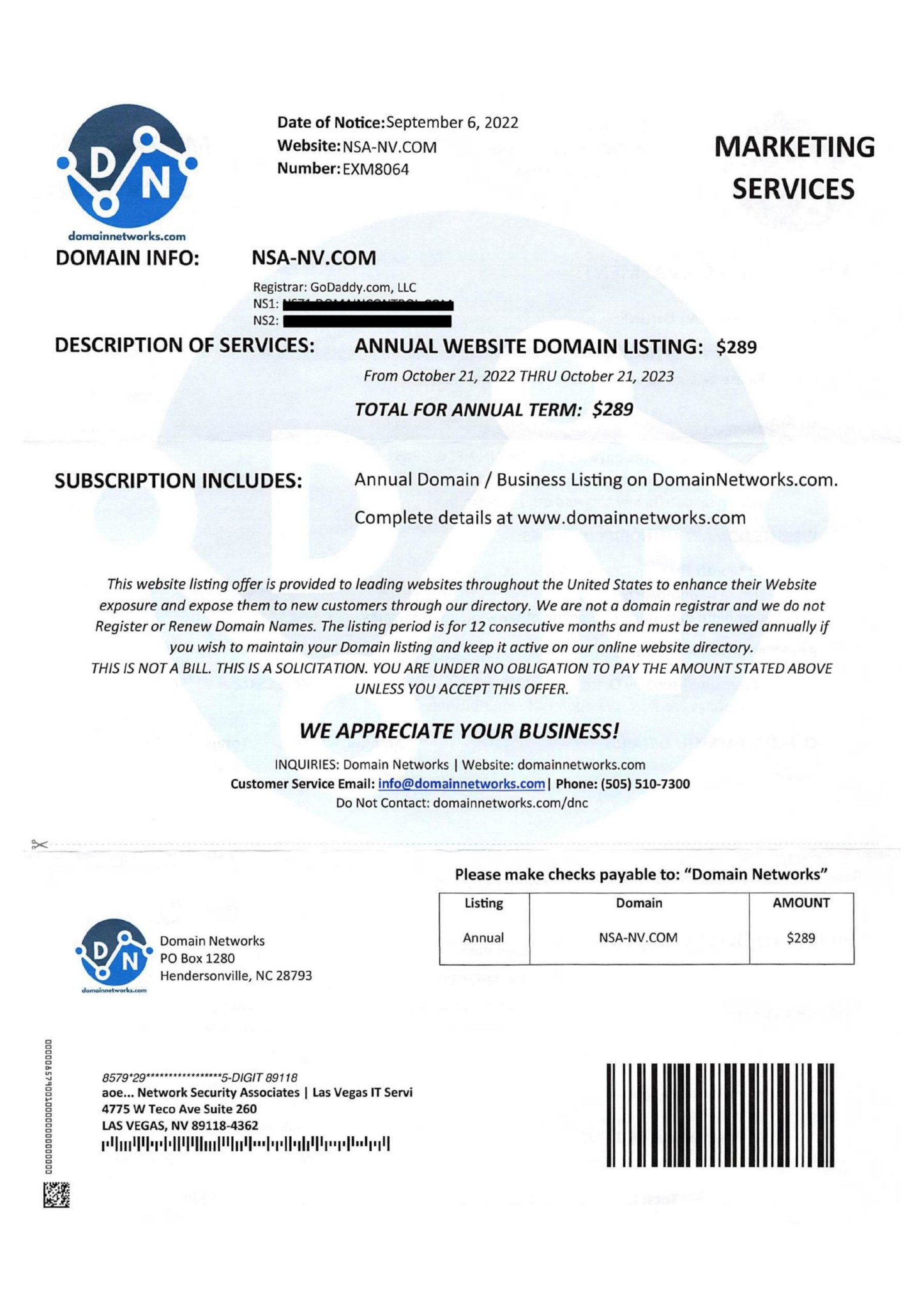
Scam of the Week: Domain Networks Invoice Scam
A new scam is targeting business owners who own and maintain their company’s website and domain. In what appears to be a legitimate invoice mailed to your business address, a phony directory company called ‘Domain Networks’ requests up to $289 for ‘listing...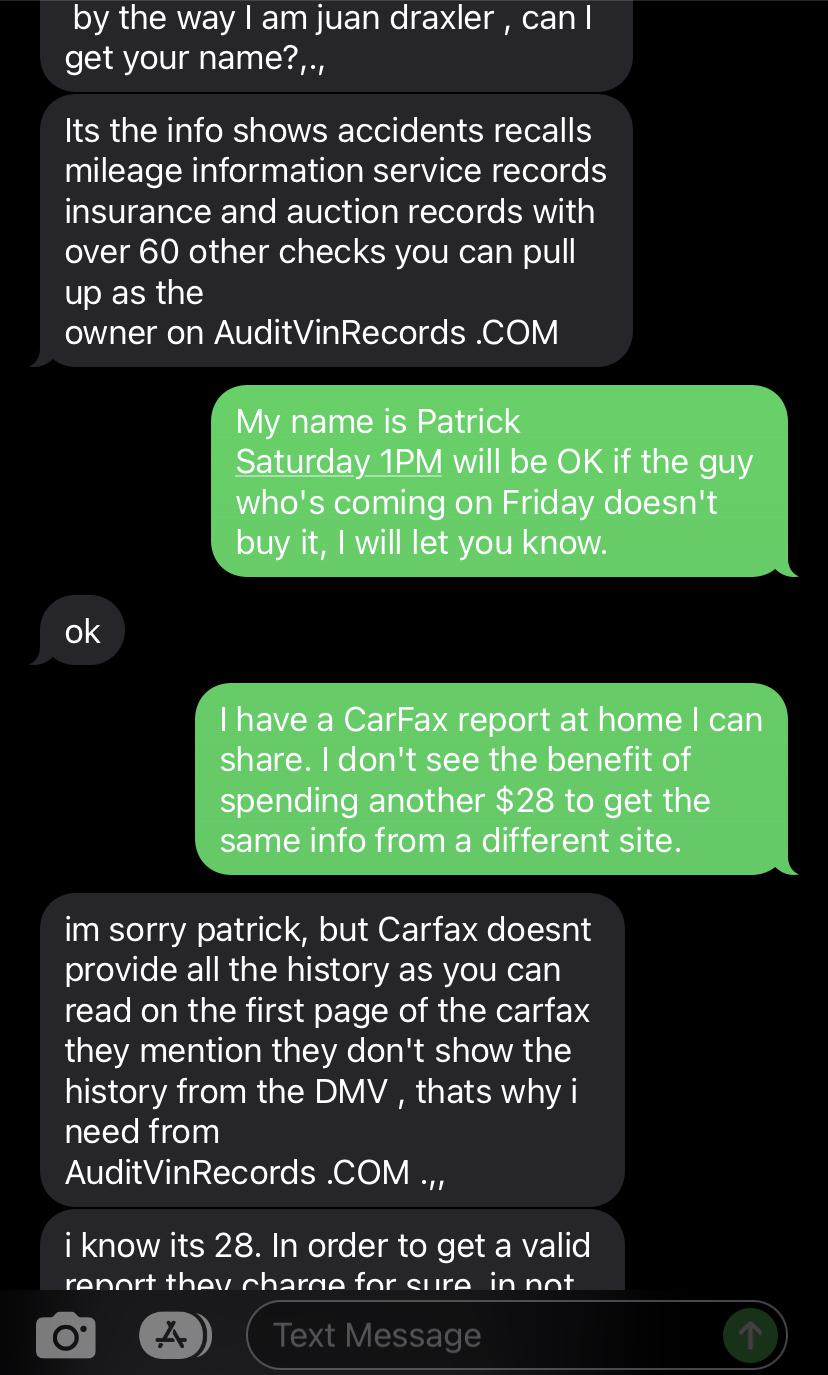
Scam of the Week: Craigslist VIN Report & Google Voice Scam
Requesting a VIN number and an auto history report is usual practice for either buying or selling a used car, especially in online marketplaces like Craigslist and Facebook Marketplace. But what if you’re selling a vehicle, and someone asks for a report from an...
