How the April 2019 Windows 10 Update Will Bolster Computer & Network Security
In April of 2019, Microsoft will issue an update for Windows 10. There isn’t a specific release date for the update, and it’s expected Microsoft will issue it gradually. If April comes and goes and you haven’t received a message encouraging you to...
Mitigating Insider Threats With Proper Healthcare IT Security
Though you may associate healthcare data breaches with hackers or digital thieves halfway across the globe, an astonishing amount of breaches are by individuals within the organizations. These threats are known as insider threats; research states approximately 58...
The True Costs of Not Implementing Cloud Security
If the upfront expenses of moving your company’s data to a cloud-based server have caused you to pause your plans, it’s time to explore the costs of not using the cloud to store your valuable information. Neglecting to move your data to the cloud can cost...
3 Essential Tips for Spring Clean Your Office
We all have that stack (or two, or three) of papers, files and things “to do” piled on our desk. We say to ourselves, “I’ll get to that when I have a spare moment.“ But, in today’s fast-paced work environment, spare moments are hard to find. Here are 3 simple office...
5 Network Security Tips for Preventing Data Breaches
A data breach is costly for any organization. Not only does it cost your company money, but it lowers consumer trust in your brand. Here are some simple tips to improve your network security and prevent data breaches: Necessary Protocol to Enhance Your Network...
3 Rules to Avoid Phishing Scams With Secure Network Services This Tax Season
Tax season is associated with a host of phishing scams; some reappear each year, while others are relatively new. These scams are designed to steal money or sensitive information. Keep your info and funds safe with secure network services and by following these...
Windows 7 End of Life & What it Means For Me
Windows 7 and Server 2008 end of life means that Microsoft will no longer improve the product, accept warranty claims, or provide non-security hotfixes. This is known as mainstream support. It will continue to offer bug fixes and security updates through January 14,...
Bring Your Own Device (BYOD) Best Practices and Proper IT Services
With smart devices surging in popularity, it’s inevitable your employees may want to use their own mobile phones for work-related tasks. Allowing them to do so has multiple benefits, but there are also a few risks your company should acknowledge and have proper...
Network Security Solutions: Developing a Disaster Recovery Plan – Pt. 2
Once your company implements the infrastructure to securely back up its data and add layers to your network security, it’s time to tend to other aspects of your disaster recovery plan. Keep your company’s recovery time objective (RTO) and recovery point...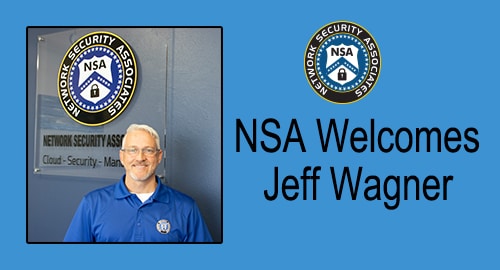
NSA Welcomes Jeff Wagner
Network Security Associates welcomes Jeff Wagner as a Senior Solutions Consultant. “With more than 10 years of Technology & Information Security experience, we know that Jeff’s skills will add value to the already experienced team here at NSA. “I surveyed...