The cyberattack on Change Healthcare has sent shockwaves through the healthcare industry, disrupting operations for pharmacies, providers, and patients. In this blog, we discuss the impact of the cyberattack as well as the drama surrounding it.


The cyberattack on Change Healthcare has sent shockwaves through the healthcare industry, disrupting operations for pharmacies, providers, and patients. In this blog, we discuss the impact of the cyberattack as well as the drama surrounding it.

As technology advances, so do the challenges it brings. With the growing complexity of technology in our lives, businesses are turning to Managed IT Services to optimize their IT operations.

Explore the differences between Microsoft Copilot and ChatGPT, two leading AI tools revolutionizing productivity. Discover their unique features, integration capabilities, and pricing to choose the right tool for your work needs.

UltraTax is a comprehensive tax compliance software designed to simplify and streamline the complex processes involved in accounting, tax preparation, and payroll. Developed by professionals for professionals, UltraTax offers a robust platform that ensures accuracy, compliance, and efficiency in managing financial obligations.

In this blog, we will delve deeper into the features of Microsoft Copilot within some of Microsoft's most popular apps.

Copilot seamlessly integrates into your daily Microsoft 365 toolkit. In this blog we take a deeper look into what exactly Copilot for Microsoft 365 is.
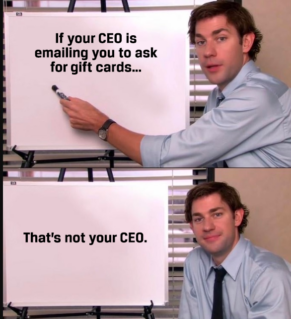
We are witnessing a surge in the cyber threat known as "CEO Fraud." Learn what this growing cyber threat is and how to protect yourself and your business.

Embrace a tech-driven start to the new year! Uncover the resolutions that will guide your business toward success in 2024.

As the year concludes, fortify your business against cyber threats. Discover the key strategies for a secure and stress-free holiday season.
Unravel the OpenAI turmoil – CEO ousted, Microsoft's move, and the clash over AI's path. A high-stakes tech drama with far-reaching consequences.

Businesses can still be denied a policy even if they are prequalified for cyber insurance. Get an MSP to do work for you.

The risk of cyberattacks is increasing. Businesses can mitigate these attacks by purchasing cybersecurity insurance for their industry.